Hacker Evolution Collection – Review
by Adam
|
I quite enjoy typing. I certainly enjoy computers. I definitely like the hit 1983 film which launched the career of Matthew Broderick, War Games and, as such, I happen to be in a lot of luck as I have the pleasure of bringing to you a review of exosyphen studios Hacker Evolution Collection, typed on a computer, whilst watching the hit 1983 film War Games.
The hacking game is nothing new. The idea has ultimately evolved from the text adventures of days sadly gone by and then trickled its way back into gaming culture through nifty browser based html or flash games, mini game easter eggs and the dedicated few who challenge the cult classic Uplink in the retail market. Having been originally released in 2007, the Hacker Evolution series has since been graciously decorated with a full sequel, along with expansion packs for each version, warranting a complete ‘Collection’ release this month.
For the un-initiated, Hacker Evolution is an entirely console based game relying on the entry of computer based commands, issued in text form only and carefully selected in order to complete mission objectives. There is no reward given to a proficiency in typing speed or efficiency beyond an arbitrary time elapsed high score and the game is welcoming to all, being less dependent on skill and more reliant on a solid logical mind.

How about a nice game of chess?
Puzzles vary from the destruction of virtual property, theft of digital resources and detection type mysteries which see you combing through servers to uncover who else is hacking their way through cyberspace. All of this is tied together into the perspective of Brian Spencer, a former intelligence agent living in the year 2015 who left the spying game a few years previously after having failed a mission, followed by the death of his whole family in a freak car accident. ‘The cause remains unclear’ and this looks like exceptionally bad writing on my part. Sadly this is simply the character profile as presented to you by the game’s Romanian development team and I’ll spare you any further criticism of some odd translations and redirect your focus back to the game itself.
Brian’s personal story actually bears no relevance to the game’s central plot line and isn’t actually a mystery to be solved. Your family is dead and you happily retired to your own private island until the Federal Services Agency got in touch, asking you to do a little freelance work for them by helping to track down a hacker who managed to get inside the New York Exchange. Tracking down the culprit leads you on a multistage, nine mission campaign which, again, has very little to do with the game’s opening cut-scene in which exosyphen details how the Xenti Corporation has developed data transmission speeds so fast, it has caused the space time continuum to rupture and allow for files to be received before they were even sent. With this apparently being some sort of problem, the developing company created an AI to control package delivery, which, as I’m sure you have already guessed, spread throughout time and alternate realities, giving it unrivalled processing power, evolving beyond its programming and falling out of the control of its creators. Thankfully it doesn’t want to kill anyone, it just wants to survive.
I’ll give you a moment to digest all of that.
It’s a lot to take in and even more so to then completely ignore. Whilst Hacker’s internal mission plot lines are compelling and follow on from mission to mission, the weird world of a dead intelligence agent’s family and super computers which occupy simultaneous dimensions is beyond a sub-plot and more akin to an episode of your favourite TV show where the main character wakes up at the end (only he’s waking up on his own private island and his family are still dead). It certainly helps to give you a sense of paranoia however, crucial to the success of a good hacking game. If you don’t feel as though at any moment, a time travelling AI can manipulate company records and have your family murdered, well then you’re not going to get as much of an experience out of this and you may as well pretend you’re just doing some bizarre admin work for a temping agency.
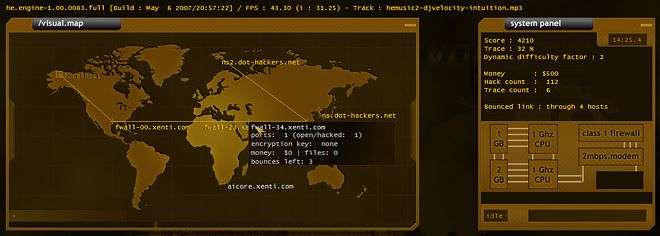
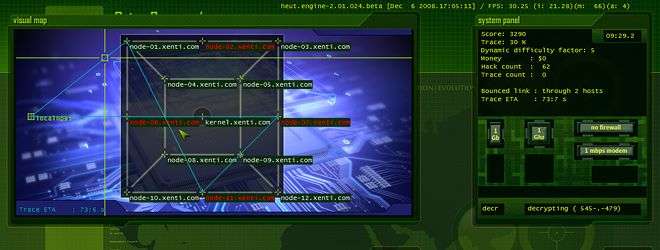
 Back to the game itself; Hacker Evolution presents itself as basically as it needs to. The User Interface comprises of a console window in which for you to input commands and review data, a global map representing the geographical locations of servers around the world, a Systems Panel detailing your computers hardware, active operations and connection information and an inbox for you to receive helpful e-mails. It’s a simple design with no complications, no extra interfaces to flit between or any information hidden in a sub-menu. At best, you’ll only ever find yourself tapping PgUp and PgDn to scroll through the text displayed on the console.
Back to the game itself; Hacker Evolution presents itself as basically as it needs to. The User Interface comprises of a console window in which for you to input commands and review data, a global map representing the geographical locations of servers around the world, a Systems Panel detailing your computers hardware, active operations and connection information and an inbox for you to receive helpful e-mails. It’s a simple design with no complications, no extra interfaces to flit between or any information hidden in a sub-menu. At best, you’ll only ever find yourself tapping PgUp and PgDn to scroll through the text displayed on the console.
The only dynamic aspects of the UI occur when trace programs are ran against your connection, creating a visual representation of just how long you have before your location is discovered. Failure to complete an operation before the trace is made can result in a total mission failure and so the added little touch of being able to see how long you have left really does help to build the tension.
In the follow up, Hacker Evolution: Untold the UI becomes more dynamic, simply by making the map pane display images as a background which is more relative to the mission, swapping the traditional world map out for more immediate locales. It’s a minor addition to the series but when tasked with hacking a traffic light system to slow down the hit-men hired by the company you just hacked into whilst sat in a cafe across the street from their offices, the tiny visual addition really does make for a more immersive experience.
 |
 |
 |
With such a simplistic UI, it should come as little surprise to learn that control is implemented in a similar way. The mouse cursor will find little to do beyond speeding up a few commands relative to the map pane or flicking through emails in the inbox; all control is literally at your fingertips, right there on your keyboard.
If you’re anything like me, the only action your keyboard will have ever really seen when gaming exists around the WASD keys. It’s the default position my hand moves too whenever I sit at my keys. Occasionally the 1-4 keys see some use, Shift, Ctrl and Alt make an appearance as a modifier and the spring in my space bar takes a light pounding as a I bounce around like a bunny on crack laced carrots. To make use of the whole keyboard in a game is as alien a concept to me as getting up in front of my 360 and flailing my limbs randomly in the hope I accomplish something.
Having to fully type out a command rather than just activating hotkeys or clicking on an action bar helps you feel right at home in your new role as a widowed former intelligence agent and this more manual execution of abilities has a genuine, initial feeling of gratification to it. There’s something deeply satisfying in the input of commands where the product of your actions was a direct contribution by you, the gamer, rather than an expression of your on screen avatar.
 That said, the magic does begin to wear thin when having typed ‘connect server-hacker.evolution.com 699′ you discover that what you were actually supposed to type was ‘connect server.hacker-evolution.com 699′ and then have to type it all out again after the obligatory stare at the screen professing that you did absolutely nothing wrong. It’s at this point when you begin to question the quirky Windows 1.0 approach to a future world where A.Is exist in both space and time (a market which even Wal-Mart are yet to enter) why it is you don’t have the ability to highlight text from within the console, using your mouse to right click copy or left click paste nor to be able to click highlight any part that’s wrong and quickly correct your mistake.
That said, the magic does begin to wear thin when having typed ‘connect server-hacker.evolution.com 699′ you discover that what you were actually supposed to type was ‘connect server.hacker-evolution.com 699′ and then have to type it all out again after the obligatory stare at the screen professing that you did absolutely nothing wrong. It’s at this point when you begin to question the quirky Windows 1.0 approach to a future world where A.Is exist in both space and time (a market which even Wal-Mart are yet to enter) why it is you don’t have the ability to highlight text from within the console, using your mouse to right click copy or left click paste nor to be able to click highlight any part that’s wrong and quickly correct your mistake.
Whilst the initial feeling is bizarrely authentic to the world of hacking, you soon find yourself wondering if the iPad is yet to make it to the Romanian markets. The lack of functionality in the controls doesn’t quite seem to fit the game’s 2015 setting despite the inclusion of time saving functions such as the TAB key to auto-complete partially typed commands or the ability of the Up/Down keys to cycle through anything you previously entered. These functions are essential to stave off the irritation of having to repeatedly enter the same lengthy commands but unless you’re already familiar with games of this ilk, don’t expect to be told that these functions even exist.
Which leads me neatly on to the game’s tutorial. Newcomers to the field would certainly be put off by the lack of visual applications and the idea of navigating a world purely through the correct use of command lines. Typing ‘HELP’ into the console generates a list of input commands, their function and an example of its usage. Most commands are fairly self explanatory with ‘CRACK’ providing the ability to bypass password protection on hosted computers and ‘DECRYPT’ breaking any encryption protection on the servers network. As the missions become more complex, more console commands come into play, further complicated by commands which are strictly context specific.
It is hoped that the tutorial would gently break you into the world of cyber crime and detection but the experience is perhaps more akin to being given a tour through the Musée du Louvre by a drunk Terry Wogan, on a fighter jet during a Parisian blackout. Whilst there are no time constraints on the tutorial, the manner in which the tutorial is delivered (through procedurally generated tooltips appearing in your teeny tiny inbox window) only directs you through the level, in no way offering any explanation of any of the tasks you need to perform that you’re ultimately performing in preparation for tackling the main game. You are simply told ‘How’ to complete the mission objectives, leaving the ‘What, Who, Why and Where’ completely up to you.
It’s a cruel introduction and once you begin the game proper, you really will be making good use of the ‘HELP’ command. I even found myself restarting the game several times in an effort to better understand the available commands but it still took me a trip around Google to find more approachable, user friendly help. I have criticised games in the past which have perhaps gone too far in holding your hand through a games introduction, stopping to patronisingly teach, refresh and retrain every little detail, but I can see how many would be put off by this rather more sadistic approach.
As an example, the game eventually requires you set up ‘Bounced Links’ – a linking of servers prior to the connection you intend to make which increases the time before your location is traced. It’s a fairly key aspect of the game as 50 percentage points will be added to your total trace amount should you fail to complete a command before the trace is made. With a 100% trace resulting in mission failure, you really do need to have a good grasp of how to bounce your signal so that you can safely crack longer passwords or decrypt tougher servers. Sadly the instructions are a little vague and ‘BOUNCEHELP’ providing little more than a splash of water in a pint of whiskey. With each server being restricted to a set number of ‘bounces’, using links surplus to a requirement you’re unaware of can result in creating an impossible situation further along the mission where you find yourself unable to complete a command without incurring that 50 point fail trace.
 |
 |
 |
With no avenue to pursue any training, you simply find yourself experimenting like the game doesn’t matter until you eventually get the hang of it and then can re-start the campaign, convincing yourself that you’re ready to tackle the game properly. Once you’ve subjected yourself to this rather torturous approach to self tutorial, you can then start to appreciate the complex nature of the game that separates it from rivals within this niche sub-genre of the PC gaming world.
You need to be able to understand the capabilities of your system and be confident that you can complete a task using what you estimate to be the bare minimum of bounced links, each carefully selected so that when it comes to connecting to a server along that link, you still have a viable chain in order to delay that all important trace. It gets a little close at times with some actions completing 0.2 of a second before the trace can be made but it sure does feel rewarding in those early stages, in the days before you have transferred enough money from servers to your own bank account in order to purchase upgrades for your machine.
Beyond your own Einstein like mathematic calculations, you then need to have a Sherlock Holmes eye for the details and the cunning to unravel the mystery behind each mission. Again, this isn’t so much a skill you are slowly made to realise you have but more one you are shown to be in dire need of a weekend watching Poirot. The very first mission will punish you severely for failing to register an altered document, signed by a group of hackers. It’s a tiny alteration to the original that is presented to you, with no indication given that the document had ever been tampered with but in failing to notice it and deduce that the group of hackers must have a server that they could have hacked from, you would not gain access to their server to use as a bounce-link, nor the information and finances contained on their server.
 The game is positively littered with these tiny little requirements that elevate Hacker way beyond a basic console command hacking game and very much into the world of puzzle and strategy. With a little acknowledgement already made to the compelling internal plot lines of the missions, the game really does challenge you to beat it so that you can learn more and happily punish you for simply not being up to the task.
The game is positively littered with these tiny little requirements that elevate Hacker way beyond a basic console command hacking game and very much into the world of puzzle and strategy. With a little acknowledgement already made to the compelling internal plot lines of the missions, the game really does challenge you to beat it so that you can learn more and happily punish you for simply not being up to the task.
Beyond the initial campaign to investigate the mysterious crashes in the New York Exchange and other key institutions around the globe, the Reinsertion expansion picks up from where Hacker Evolution leaves off, providing three complete missions to explore. In Hacker Evolution: Untold, you return to the life of Brian Spencer only this time, you’re the one being investigated. As well as having to discover who it is that is trying to track you, the game becomes even more difficult by simultaneously tasking you with delaying the same shadowy organisation from finding you – a very simple story element that doesn’t alter any of the existing gameplay but really draws you deeper into the game’s world. If you’re not content with your fill after all of that the, so far, final addition to the series rounds off the collection with Hacker Evolution: Untold – Flight Zero, another three mission add-on pack in which a mysterious operative waltzes into and steals technology from the corporation you just closed down in an attempt to restart the whole project. Of course you’re the only man for the job and so they drag you out and beat you with a stick until you start to yield some results which contribute towards the unmasking of the Scooby-Doo villain.
 Again, it’s not Shakespeare, but once you get started you just can’t help but to fail the mission majestically and come right back at it with a renewed vigour, determined to get into the next mission and find out what’s really going on. Replay wise, Hacker will hold very little extra for you with no greater reward than achieving the mission objectives more flawlessly than your first attempt and earning a higher score in order to place better on the global leaderboards. There are no moral decisions to be made here with no endings other than your predetermined fate which is something of a missed opportunity considering that there’s a time travelling computer somewhere on the planet.
Again, it’s not Shakespeare, but once you get started you just can’t help but to fail the mission majestically and come right back at it with a renewed vigour, determined to get into the next mission and find out what’s really going on. Replay wise, Hacker will hold very little extra for you with no greater reward than achieving the mission objectives more flawlessly than your first attempt and earning a higher score in order to place better on the global leaderboards. There are no moral decisions to be made here with no endings other than your predetermined fate which is something of a missed opportunity considering that there’s a time travelling computer somewhere on the planet.
For those still hungry for more, the game features full mod support and comes packaged with its own editor, installed into the game’s directory and is dutifully supported by the dedicated community on exosyphen studios forums. It makes for a nice addition to the game that I’m sure will see a renewed sense of creativity after the collection’s release.
Beyond the major criticism of Hacker Evolution’s almost vertical learning curve, little more can be ill spoken of the game. It’s soundtrack is a little jarring to anyone who isn’t into any Techno/Trance music but it’s nothing that can’t be disabled in the options and rectified with BBC Radio 2 or a Jive Bunny Mega-mix. The sound effects are as simple as the UI, with typing noises played as text is presented to you, beeps to confirm data entry and more angry and urgent beeps to warn you of impending doom. It may not sound like much but it’s hardly an experience that would benefit from Skywalker Sound THX Dolby Digital 8.1 Surround Brain Sound. Those who are at first hoping for another open world to hack through and take randomly generated tasks to raise notoriety and cash as found in Uplink will be at first disappointed by the game’s narrow direction but immediately lured in by the same challenge experienced by those new to the genre. It could certainly benefit from a better tutorial but where would the sadomasochistic fun be in that?
Pros- A great, unique experience
- Simply presented
- Rewarding
- Compelling Missions
- Little replay value
- Incredibly daunting for newcomers
- Extremely challenging for the faint of heart
- Would benefit from more advanced functionality
The Hacker Evolution Complete Collection is niche product in a niche market. That said, it's not one to turn your nose up at and not one to punish for bending your nose a little out of shape if you do make time for it. The games challenge doesn't lie in any failure on it's own part but simply from within those willing to invest their time in it. The experience on offer is a carefully directed and well thought out mystery for you to solve. It's closest rival in the market may make for a more approachable game than exosyphen studios creation, but the two are catering to very different tastes. If you're looking for a good, solid puzzler with a leaning towards those with an open, strategic mind, look no further.
If you'd rather have the experience without the brain hemorrhaging, well then War Games is available on DVD these days. Poor Matthew Broderick, to think he had a bright career in front of him back then.
Last five articles by Adam
- Party Pooper
- Battlefield 3 - Review
- Red Orchestra 2: Heroes of Stalingrad - Review
- Burnout CRASH! - Review
- Dead Island - Review


















I always fancied myself as a bit of a hacker. It’s 100% Matthew Broderick’s fault too as my friend in primary school used to hang around the Bearsden Rio cinema at weekends while his mother managed the place. I remember one particular weekend they were running “War Games” and “Lone Wolf McQuade” on their two screens and I was there with my friend Cameron and his sister for the entire Saturday. Neither of us fancied the Chuck Norris movie, as he just looked like a weirdo and nothing much has changed on that score, so we watched War Games. All day. And all night. From 10am until around 8pm we did nothing but watch War Games over and over… and it was well in the world that day.
The Hacker games look like they’d perhaps rekindle that spark for me, reignite the desire to hack in to some secret government computer to find out all the secrets like whether Cherie Blair is really an animatronic or if Gordon Brown is really Stan Ogden from early Coronation Street BUT… there is one thing that puts me off these games. One very important thing…
Typing.
From the second I sit down at my PC to start work in the morning, until whenever I’m finally able to drag myself off after the clients stop pestering me and allow me MY time, I’m typing. It’ll either be programming or emailing, looking things up on Google for those who haven’t grasped the concept of search engines yet or just basically re-explaining the same thing over and over again. But it’s a lot of typing. That’s where the problem is… what little time I DO get to game in the week, I want it spent in a seriously relaxed position with two hands rested on my lap holding a controller loosely. I don’t want to be typing commands in the whole time. I love the idea of it; I love that there’s probably a huge thrill involved in managing to get through particular firewalls or security blocks, but I hate that I’d need to type it all out. I know it’s no different from a text adventure, but I’ve not played one of those in twenty five years either.
So for that reason, and that reason ALONE… I’m out.
As much as I think I could enjoy this sort of game, my frustration levels just simply would not take it, presumably culminating in my sat at my desk screaming “Why won’t you work” at my monitor.
haha @ Pix3l’s history
Nice review, had I not already tried the demo I’d have hopped off to give it a test after reading this. Having never played this type of game before, somehow missing the Uplink cultism, I was amazed by the difficult learning curve. The tutorial was less than helpful and I actually failed the first mission miserably but not sure howor why.
I guess we are used to games with fluffy feedback, easing us in and drip-feeding powers/abilities. This was an eye-opener, but sadly not in a good way. Then again, maybe I just don’t have the cognitive capacity to logically follow what’s going on….
Similar to Markuz I’d rather be playing a graphical puzzle game with the controller than fighting with a keyboard and command syntax.
Great review, but this would be a living hell for me! I wouldn’t touch it with a virtual barge pole
I enjoyed Uplink to a point, it was a bitch of a game, completely unforgiving and I could only get so far (difficulty 6 missions) before getting caught and being forced to start again. This would repeat until I finally got bored and jacked it in.
This game seems a bit more forgiving by letting you retry the missions which is good but I’m like MarkuzR in that nowadays I cant be arsed to type after getting home from work where for a good part of the day I’m sat in front of a computer typing! As such I will probably give this one a miss.
However, good review, very nicely written.
Well covered, though this one may be a little too unforgiving for me. I’m all for games not pandering and being tough, but drastically steep learning curves with almost non-existent tutorials are a touch off-putting. That said, the concept is fantastic and, with a lot of patience, it could turn out to be a pretty satisfying game. Without an accessible tutorial though, it will sadly get overlooked by many who would have otherwise enjoyed it. I like the realistic and trimmed down feel that the game seems to present and it is a cracking concept, not to mention a niche genre that I never knew existed before, nice!
Thanks for the praise guys, I can’t hope to pretend that this was anything short of a cow to review. It never bodes well that after a few hours of trying, you’re actually getting nowhere with a product you’re yet to experience.
@MarkuZ
It is a gripe that there is less interaction with the mouse and the keyboard is such a dependant method of control. It is true to the genre but as I said, it’s not the most befitting for the games setting which would imply that technology has advanced considerably but I’m unable to copy and paste? Disappointing but then again, you do spend more time thinking about what to type than actually typing making the process seem deceptively long.
@Ben
The difficulty is relentless and making a silly mistake towards the end of a mission is brutal in that it will send you right back to the start of that mission, but it really does focus you after the first several thousand times.
@Stu
I was amazed to come across just how many people that played the demo just dropped a rock on the game and ran away from it. I suppose in one sense its refreshing to know that a developer is so happy with their product they have a take it or leave it approach rather than an I’ll take your money and then leave you approach, but it really does seem counter productive from a business standpoint.
I honestly don’t think I had the puzzle solving skills on hand to deal with this at first but its really surprising how your brain just sort of starts to accept what is possible and reject what isn’t in the game.
@Tania It’s the equivalent of a PnC where you start off in a room with no way out and only a stick in your inventory. You have to pixel comb the room just to find something to interact with and even then hitting it with the stick doesn’t work. Frustrating but holds the same reward gained in any puzzler.
It’s the equivalent of a PnC where you start off in a room with no way out and only a stick in your inventory. You have to pixel comb the room just to find something to interact with and even then hitting it with the stick doesn’t work. Frustrating but holds the same reward gained in any puzzler.
Thanks
@Ste
I really do hold Uplink up as a triumph of gaming ingenuity. I think it’s fantastic in the level of freedom you have in the game that pulled me headfirst into Sid Meirs Pirates years later. A very simple premise but seemingly infinite possibilities once you let yourself go and just start doing strange things with it to see how it goes.
Hacker differs in that the missions aren’t procedurely generated or tailored to your skills. The mission is simply the mission and the solution is often confined to just one or two paths. Finding those paths are the only challenge but I couldn’t agree more that this is not a game you’re going to want to come home too. It’s not there waiting for you with a slice of cake, a chainsaw and a hug, it’s just sitting there in the corner of the room staring at you, refusing to say a word and never blinking….
@Lorna
It is mighty off putting, even when you think you have it, the game does something that makes you scratch your head and theirs no rope being dangled anywhere to help you up. I hope that exosyphen go on to produce a full new 2.0 rendition of Hacker now that the complete collection is out there and that they look to expand beyond the confines of a particularly vocal niche market. Theres an army of gamers just sitting there sending text messages and playing Texting of the bread that would get a lot out of a good puzzle solver like this, it just needs to be more accessible and more approachably presented.
Thanks again all
This game is awesome, makes you feel somewhat like a real hacker.
A brilliant review, Adam. I was laughing my head off at some points
It does sound like an incredibly niche title and one that may be too hard for me. Yeah, I don’t like games completely mollycoddling me, but I also like just enough guidance that I don’t get bored and go do something else.
Still, sounds like a fantastic title and I hope it does well!
Also, the opening image with Benbot and Pix’s internet history is genius.
Full credit for MarkuZ for turning it into an image, it was otherwise just a mass block of text that just sat at the head of the article Made me megalulz seeing it as a cmd.exe prompt.
Made me megalulz seeing it as a cmd.exe prompt.
Thanks Ed
Since War Games Matthew Broderick did save New York from Godzilla with the help of the cast of the simpsons and Leon though – you’ve gotta give him that at least.
I remember watching you play the original version of this years ago, I could never get my head around it. It was like watching somebody play that teletext game bamboozle when your TV aerial was rubbish. Maybe a little bit shiny-er than that but you know what I mean.
It’s a cool game though and the sort of one that makes you look like a god when you’re playing it right.